Continuous Security Validation Against Real-World Attacks
Identify & Eliminate Exploitable
Risk Before Attackers Strike
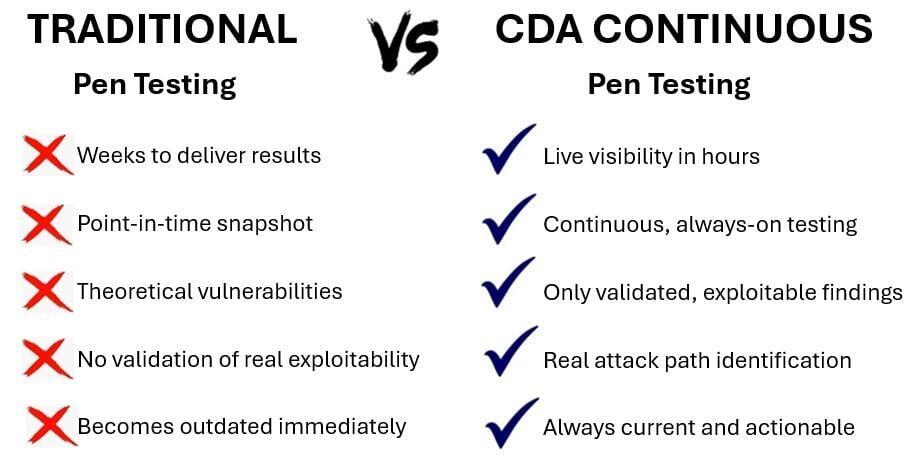
Traditional penetration tests show you where you were vulnerable.
We show the risks attackers can exploit right now
—and help you eliminate them continuously.

"Audit passed. No setbacks.”
— Ken Weeks, Newforma

“Security approved. Deal secured.”
— Regina Foti, Protos Security

“Critical gaps identified and resolved.”
— John Gojuk, 3 Story Software
Outdated Pentesting
Traditional pentesting is slow and delivers outdated, point-in-time results.
A New Standard: Continuous Security Validation
Continuous security validation replaces outdated testing, aligning security with how attackers actually operate—it’s a fundamental shift, not an add-on.
Live Attack Paths. Real-Time Alerts
We deploy AI-driven platforms to continuously simulate attacks, exposing real vulnerabilities and active attack paths.
Real Exposure. Real Elimination
No waiting weeks for static reports—risk is identified, validated, and prioritized immediately, enabling faster remediation and reduced exposure.
Human Expertise. Not Just Automation
Technology finds risk—experts make it actionable. We break down attack paths, prioritize remediation based on exploitability, and deliver executive-level insight that drives action.
How It Works in Your Environment
Continuously adapts across cloud, SaaS, and hybrid environments, identifying new exposures as they emerge.
Our platform simulates real attacker behavior to uncover true risk. Expert-led onboarding is fast, low-friction, and integrates seamlessly into cloud and DevSecOps workflows.
From Identification to Remediation
Why Cyber Defense Advisors?
Our Penetration Testing team is led by seasoned military operators with deep offensive security expertise, delivering real outcomes—not just analysis. We operate with the discipline of high-stakes environments, working alongside your team to execute and achieve mission objectives.
Who We Serve
We work with security-mature teams, cloud-first companies, regulated industries, and private equity-backed firms focused on continuous validation, risk reduction, and protecting value.
Compliance-Ready Reporting
Aligned with SOC 2, ISO 27001, PCI DSS, HIPAA, FedRAMP, and cyber insurance requirements. Structured to support audits, streamline compliance, and demonstrate continuous security validation.
Meet Our Team

Francis Schmuff | Executive Sponsor

Renee Jones, Ph.D. | Program Manager

Bryan Siegel | Director of Compliance
Comprehensive Coverage Across Your Environment
Continuous security validation runs across the systems and environments where real risk exists.
Applications & APIs
Cloud Environments
Internal & Authenticated Access
DevSecOps & Modern Infrastructure
Rapid Validation When Needed
How It Fits Together
Why This Works
Maintains a continuous testing model while covering API, cloud, DevSecOps, internal, and rapid use cases.
Removes the service menu approach and delivers a single, integrated system instead of separate offerings.

